Introduction
If you’ve been around enterprise IT for a while, the old security model probably still feels familiar.
You had a network you controlled. A data center. Clear boundaries. And most of the security effort went into protecting that edge. Firewalls, VPNs, segmentation, build a strong enough perimeter, and you’re in a good place.
And to be fair, that approach wasn’t wrong. It worked for the kind of environments we had back then.
But it doesn’t really hold up anymore.
The moment applications started moving to the cloud, users stopped being tied to a single location, and services began talking to each other over APIs, that clean “inside vs outside” model started to break. Not overnight, but steadily.
At this point, it’s hard to even define what “inside the network” means.
Attackers figured this out pretty quickly. Instead of trying to break in through infrastructure, they go after identity. It’s usually easier, and in many cases, quieter. If you can log in, you don’t need to hack anything.
That shift is exactly why identity has moved to the center of security conversations and why Zero Trust keeps coming up.
The Network Isn’t a Trust Boundary Anymore
One of the biggest mindset shifts is realizing that network location just isn’t a reliable signal anymore.
You can have a perfectly legitimate user logging in from a home network on a personal device. At the same time, an attacker using stolen credentials might appear to come from a “trusted” environment.
From the system’s point of view, those two situations can look surprisingly similar.
So the question changes. It’s no longer “is this request coming from inside the network?” but rather “does this request make sense given everything we know about it?”
That’s a very different problem to solve.
Zero Trust
“Never trust, always verify” is the usual tagline, but it doesn’t really capture how this works in practice.
Zero Trust is less about distrust and more about not making assumptions.
Every access decision is based on context. Who is the user? What device are they on? Is this behavior normal for them? What are they trying to access?
And importantly, the answer doesn’t have to be just yes or no. Access can be adjusted. Sometimes it’s seamless. Sometimes it requires extra verification. Sometimes it’s blocked.
There’s also a practical side to it: limit what can go wrong. If an identity is compromised, the goal is to make sure the blast radius is as small as possible.
Because realistically, preventing every compromise isn’t something we can rely on.
Identity Becomes the Control Plane
In Microsoft environments, you see this very clearly with Microsoft Entra.
It’s no longer the network deciding what gets in. It’s the identity system.
Every authentication request flows through Entra, policies are evaluated, signals are checked, and only then does access happen. It’s effectively the decision engine sitting in front of everything else.
Once you start thinking about it this way, the architecture changes a bit in your head. The network becomes just another signal, not the control point.
Passwords Are Still a Problem
Even now, a huge number of incidents still come down to compromised credentials.
And passwords, despite all the rules we’ve built around them, are still easy to phish, reuse, or leak.
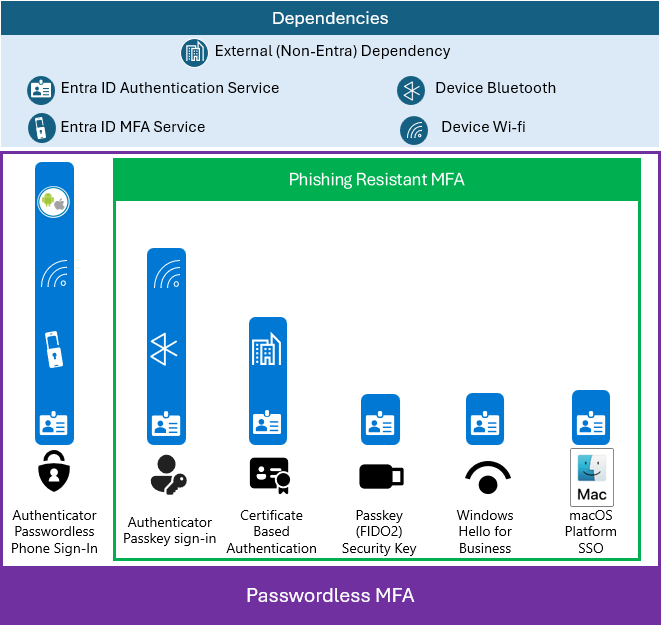
That’s why passwordless authentication is getting more attention. FIDO2, passkeys these approaches remove the shared secret entirely. The private key stays on the device, and authentication is based on cryptographic proof.
It’s not magic, but it does remove one of the most commonly exploited weaknesses.
Context Matters More Than Ever
One thing that becomes obvious pretty quickly is that authentication alone isn’t enough.
A valid login doesn’t automatically mean safe behavior.
This is where Conditional Access really earns its place. It adds context to the decision. Is the device compliant? Is the location expected? Does the sign-in carry any risk signals?
Most of the time, users don’t even notice it working in the background. But when something is off, it steps in, maybe with MFA, maybe by blocking access entirely.
That adaptive behavior is what makes it effective against modern attack patterns.
The Identity Layer Is Now a Target
As identity becomes more central, it also becomes more attractive to attackers.
And not always in obvious ways.
Sometimes it’s not about logging in as a user, but about setting up persistence. Registering an application, requesting permissions, generating tokens, things that don’t immediately look suspicious but allow long-term access.
If governance around these areas is loose, it can be surprisingly easy to miss.
Token Lifetime Is a Real Consideration
Tokens are great for performance and scalability, but they introduce a timing issue.
Once issued, they’re valid for a while, even if something changes in the meantime.
Continuous Access Evaluation helps reduce that gap by allowing systems to react in near real time. If risk changes, access can be revoked without waiting for the token to expire.
It’s one of those behind-the-scenes improvements that makes a big difference operationally.
Not All Identities Are Human
It’s easy to focus on users, but in many environments, service identities outnumber them.
Applications, automation, pipelines, all of these rely on identities that often have persistent access and don’t go through the same visibility checks as users.
If one of these gets compromised, it can be difficult to spot.
That’s why workload identities need the same level of attention, especially when it comes to permissions and monitoring.
Privileged Access Still Needs Extra Care
Some things don’t change. Admin access is still high risk.
What has changed is how we manage it. Instead of permanent roles, the trend is toward just-in-time access. You activate privileges when needed, and they’re removed afterward.
It’s simple in concept, but it reduces exposure quite a bit.
Detection Starts With Visibility
One advantage of identity-centric security is the amount of signal it generates.
Logins, access patterns, behavioral anomalies — all of this can be analyzed. And when something doesn’t look right, it often shows up there first.
Response actions also tend to revolve around identity. Disable an account, revoke tokens, terminate sessions — you can shut down a lot of activity very quickly this way.
Closing Thoughts
The move to cloud didn’t just shift infrastructure. It changed what we can rely on.
The network is still there, but it’s no longer the foundation of trust. Identity has taken that role, whether we explicitly design for it or not.
Zero Trust is really just a reflection of that reality.
And at this point, treating identity as anything less than the core of your security architecture is probably where most of the risk starts.